Specialist Training & Readiness
Practical labs, field simulations, and executive briefings tailored to the people who guard your mission.

Practical labs, field simulations, and executive briefings tailored to the people who guard your mission.
The problem
Slide decks and multiple-choice quizzes create a false sense of readiness. When a real incident hits — a phishing lure, a hostile approach at a hotel, a media ambush — people fall back on instinct, not policy. The gap between knowing and doing is where breaches live.
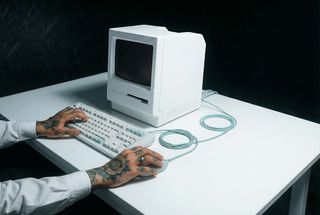
HAWK's specialist training programmes replace passive learning with pressure-tested muscle memory. We train the way adversaries operate — hands-on, scenario-driven, and tailored to the exact threat landscape your people face.
We turn policies into instincts. Our specialist trainers work with principals, chiefs of staff, personal agents, and remote teams to reinforce secure habits through immersive demos, live-fire exercises, and media rehearsals.
Curricula flex from one-day intensives to ongoing academies and can be delivered on-site, in secure classrooms, or virtually with equipment shipped ahead of time. Every module is built around your actual risk profile, not generic threat briefs.
Post-training, we measure retention with unannounced spot checks and simulated attacks — so you know the investment is translating into real-world readiness, not just attendance records.
Talk to the training deskHands-on labs covering phishing response, secure messaging, credential hygiene, and device hardening basics.
Route planning, hotel sweeps, panic workflows, and situational awareness for principals and protection staff.
Crisis comms drills, interview coaching, and coordination with our Privacy & Reputation desk.
Tabletop walkthroughs, escalation-chain rehearsals, and live breach simulations for your operations team.
Secure account setups, phishing breakouts, password management, and encrypted collaboration drills.
Advance planning, hotel/venue sweeps, duress comms, and cross-border device procedures.
Media interactions, social amplification, and rapid response coordination when narratives shift.
A team that reacts on instinct, not instruction — and proof that the training sticks long after the session ends.
Every module is built from your actual risk profile — not off-the-shelf slides.
On-site, virtual, or hybrid with equipment shipped ahead. Works across time zones and travel schedules.
Simulated attacks and spot checks confirm that knowledge translates into action under pressure.
Pick the cadence that matches your team size, travel rhythm, and readiness goals.
Intensive
Series
Embedded